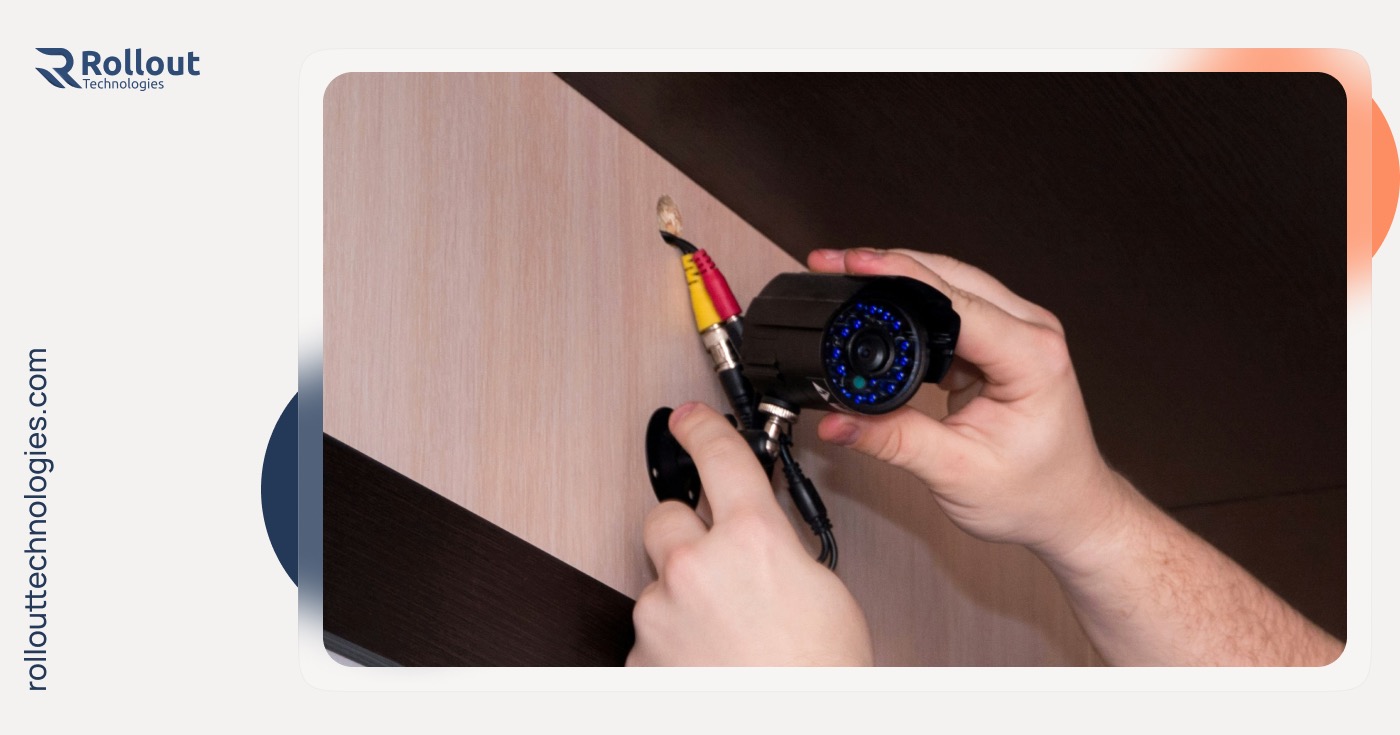
Endpoint Security
Delegate your company’s endpoints (devices) security to our team of skilled specialists, who will systematically identify and wipe out emerging threats, allowing you to focus on advancing your business towards development and success. Empower your business with our state-of-the-art endpoint security solutions in Edmonton, Canada.
Effectively Protect Each Endpoint
Data Encryption
Transparent Reporting
Scalability
Mitigate Risks with a Robust Endpoint Security Solution
A lack of complete endpoint security puts businesses at tremendous risk.
Safeguarding Your Business Against Evolving Threats

In this modern era of data-driven operations, endpoint security stands as an essential requirement for businesses highly dependent on data. Safeguarding endpoints against unauthorized access, theft, or possible loss becomes critical. This expanding gap between the knowledge and capabilities of attackers and defenders necessitates substantial modifications to endpoint defenses.
As you face increased pressure to secure your firm against numerous threats, it is essential to ensure that your endpoint defenses are genuinely effective. This may be done through seamless cooperation and interaction with the deployment of Rollout Technology. Our key aim is to promptly identify, analyze, stop, and contain ongoing attacks while also supplying timely and intuitive forensic information. You may be certain that these steps will be conducted without introducing excessive complexity to the IT environment or affecting the productivity of the users we wish to preserve.
At Rollout Technologies, we are one of the leading endpoint security companies in Edmonton, Canada, specializing in providing exceptional endpoint security for small businesses. Our staff comprises experienced IT specialists and technology enthusiasts eager to help you build a powerful, effective, and secure endpoint security solution for your complete organization, including desktops, tablets—Internet of Things (IoT) devices, mobile-devices, etc.
We understand that the security of your business’s data is paramount, and as your trusted endpoint security provider, we are committed to delivering the best possible solution to safeguard your endpoints. Our solutions are designed to protect your endpoints from a wide range of threats, including malware, ransom-ware, and data breaches.
What Do We Offer
We realize the uniqueness of every business, which is why we modify our endpoint security solutions, to suit your particular requirements.

Requirements Gathering & Security Assessment
We begin by doing a complete study of your endpoint security requirements and analyzing your existing endpoint security implementation. This evaluation helps us to find weaknesses and areas that demand improvement.
Solution Design
Our skilled team builds a bespoke endpoint security solution that matches precisely with your company goals. This comprehensive solution may comprise antivirus software, intrusion detection systems, data encryption, and other related technologies.
Proposal and Agreement
We submit a full proposal explaining the preferred endpoint security solution, replete with its features, benefits, implementation strategy, schedule, and price. Throughout this process, we communicate closely with you to resolve any issues and establish a mutually accepted agreement.
Implementation Planning
With great accuracy, we design a complete deployment strategy, defining each step needed to establish the endpoint security solution. This involves designing the deployment timeframe, software installation processes, configuration settings, and user training.
Deployment and Configuration
Our expert staff performs the deployment strategy with greatest care, smoothly installing and configuring the specified endpoint security products across your devices. This entails deploying agents or software, implementing security rules, creating access restrictions, and integrating with your current systems.
Continuous Threat Monitoring
To assure proactive protection, we develop powerful continuous monitoring systems that immediately detect and respond to attacks in real-time. This involves installing intrusion detection and prevention systems and security information and event management (SIEM) solutions.
Security Audits and Compliance
We undertake frequent security audits to check the efficiency of the endpoint security measures and ensure compliance with industry requirements. Detailed information on security posture, vulnerabilities, and recommended maintenance activities are supplied.
Continuous Improvement
We regularly analyze the efficacy of the endpoint security solution, acquire useful feedback, and suggest areas for development. Our proactive strategy covers being current of emerging threats and changing security technology, allowing us to give you proactive advice and continuous enhancements.

Technologies we use
Why Us?
Rollout Technologies is a 4+ years trusted and renowned IT Company in Edmonton that delivers top-notch endpoint security solutions for small businesses in Edmonton, Canada. We have served some of the greatest businesses in the industry and have been able to acquire amazing trust and respect from our clients over the past many years with our efforts.
With a proven track record of putting up secure and robust endpoint security solutions across different sectors, we ensure that our clients are confident when they employ us. By offering you entirely tailored services to fit the unique requirements of your organization, we assure that your endpoints are always safe and up-to-date.
We, at Rollout Technologies, have a combined industry experience of over 12 years, and we are confident in delivering the finest endpoint security solution for your business on the market. Being a reputable endpoint security service provider, we leave no margin for mistakes and leaks, ensuring the total security of your endpoints.
We also take care of the performance, security, and simple accessibility of your endpoint security solution and design a cost-effective strategy for your business.
As the leading endpoint security service provider in Canada, our place among the top ranks assures you of our unshakable dependability. We take pleasure in our genuineness and true devotion to our clients.
Empowering business with tailored cutting edge tech solutions and unwavering expertise.
Effectively protect each endpoint
Remote Monitoring and Supervision
Customized security policies
Data encryption
Incident response and disaster recovery
Compliance and regulatory adherence
Transparent reporting
Scalability
Helpdesk Service
Embark on a journey of unrivaled endpoint protection (aka peace of mind) tailored to your unique needs!
Reach Us
Discover More
FAQs
Still have questions? Learn more about our services and experience through the questions of people like you.
Endpoint security refers to the protection of specific devices (endpoints) of your organization from various cybersecurity risks, such as PCs, mobile devices, servers, and even Internet of Things (IoT) devices. It seeks to safeguard these endpoints both inside and outside of a company’s network. Antivirus software is an example of endpoint security. Another example is the use of firewalls to regulate network traffic between endpoint devices.
- Endpoint security is essential because cyberattacks can occur unexpectedly, and having protection in place beforehand is crucial.
- No business is immune to data theft, making endpoint protection software necessary to safeguard against potential breaches.
- Endpoint security ensures the protection of both customer data and company data.
- Malware can create backdoors on devices, allowing it to spread to other machines undetected. Advanced software can identify these threats early on, preventing severe consequences.
- Implementing endpoint security helps in detecting and addressing potential problems before they escalate, avoiding costly damages in the long run.
Yes, Endpoint Security can help with compliance and regulatory requirements.
- It offers auditing and reporting features to track and monitor security events for demonstrating compliance.
- Automated software updates ensure devices are running the latest, most secure versions, which is crucial for compliance.
- Endpoint management solutions provide visibility and device management tools, aiding in meeting regulatory requirements like GDPR, PCI DSS, and ISO/IEC 27001.
By aligning security practices with specific regulations and endpoint security standards, businesses can ensure they meet the necessary requirements to maintain compliance.
Yes, our flexible Endpoint Security solution can indeed scale along with your business growth and expanding endpoint environment. As your business evolves, our Endpoint Security solution will adapt to meet your growing needs and provide the necessary protection for your expanding endpoint landscape.
Our endpoint security service is priced based on the number of endpoint devices you want to protect. Contact Us today to get a free quote.
Industries We Serve
Healthcare
Real Estate
Entertainment and Media
Finance and Banking
Education
Construction
Hospitality and Tourism
Manufacturing and Industrial
Retail and E-commerce
Non-profit and Social Services
Foodservice
Transportation and Logistics
Get in touch today!
Let us help you scale your business.